IoT Botnets: Advanced Evasion Tactics and Analysis – Part 2
Por um escritor misterioso
Descrição
Nozomi Networks Labs analyzes new modification techniques malware authors use to evade detection and analysis tools.

IoTEnsemble: Detection of Botnet Attacks on Internet of Things

DNS-based anti-evasion technique for botnets detection

GoTrim botnet actively brute forces WordPress and OpenCart sites
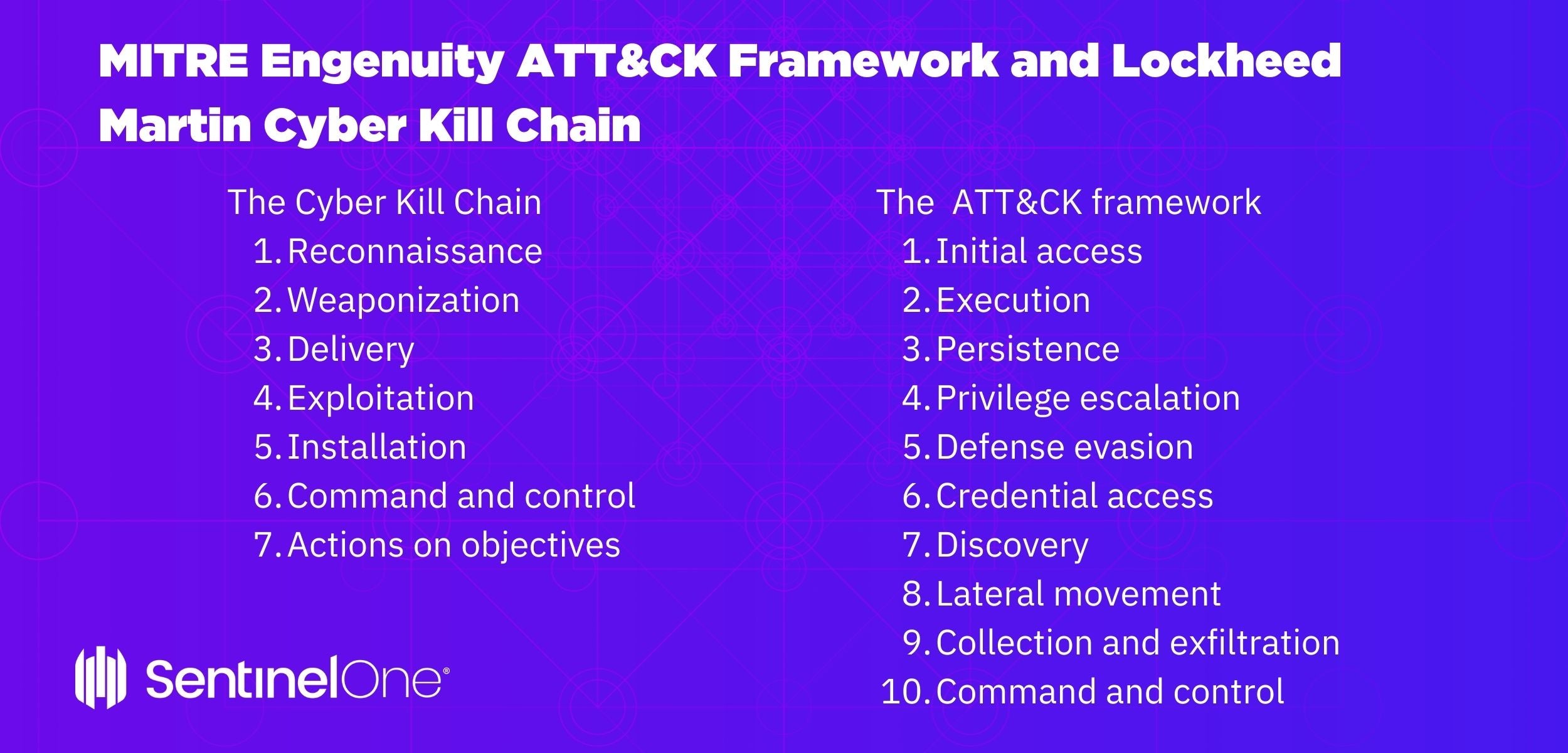
The MITRE ATT&CK Framework Explained
JSAN, Free Full-Text

PDF] A Botnets Circumspection: The Current Threat Landscape, and What We Know So Far
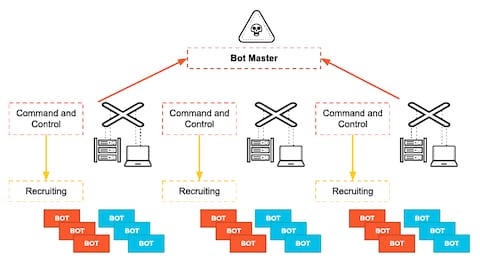
What is a Command and Control Attack? - Palo Alto Networks

A Comprehensive Survey of Recent Internet Measurement Techniques for Cyber Security - ScienceDirect

Adversaries' Evasions are Growing Faster than Defenders' Detections - Part 2
Into the Battlefield: A Security Guide to IoT Botnets - Security News
February 2020's Most Wanted Malware: Increase in Exploits Spreading the Mirai Botnet to IoT Devices - Check Point Blog
PDF) Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research
de
por adulto (o preço varia de acordo com o tamanho do grupo)