Clicks limits access to customers' personal data after cyberattack
Por um escritor misterioso
Descrição

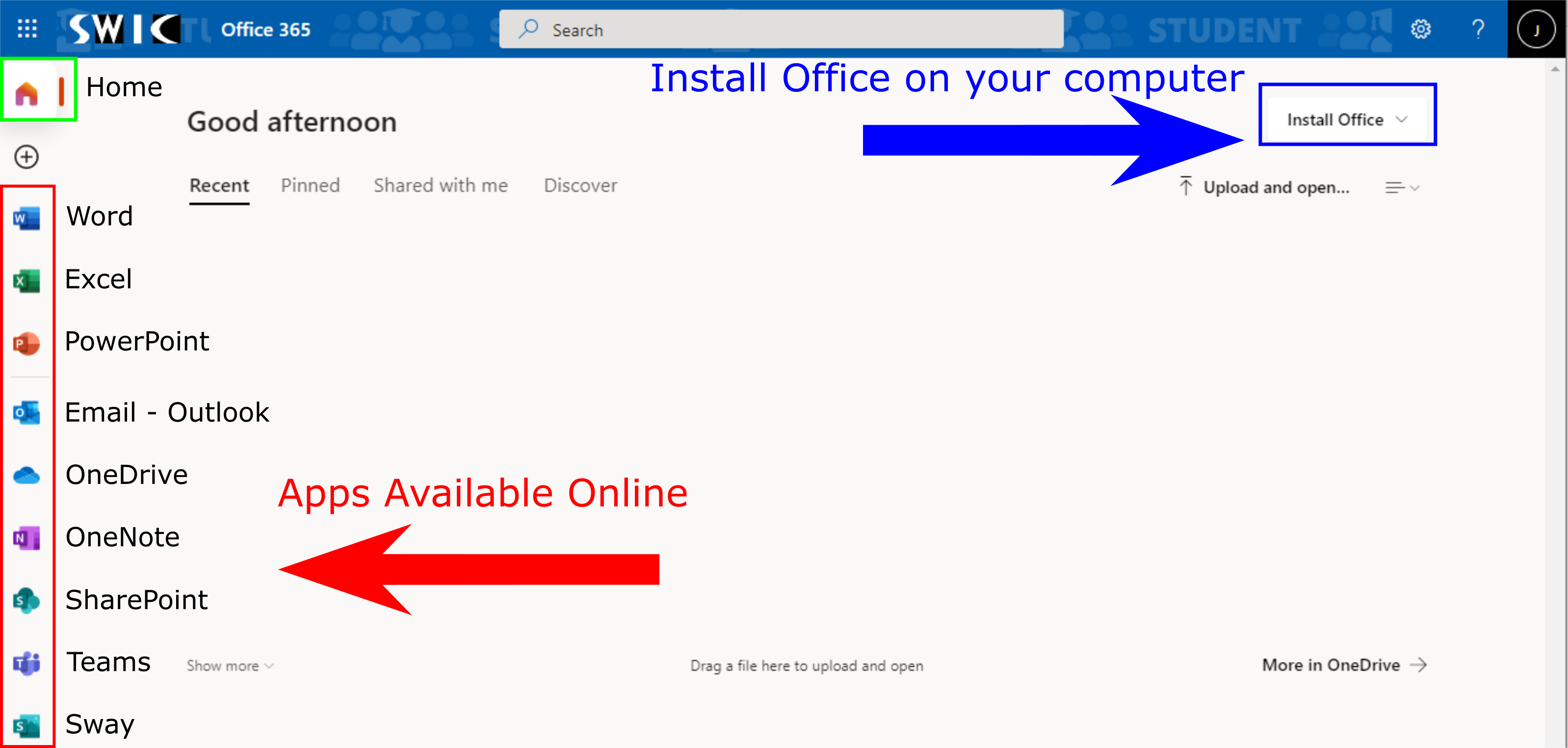
How companies can secure and protect customers' personal data
12 Cybersecurity Best Practices to Prevent Cyber Attacks in 2023
/cloudfront-us-east-2.images.arcpublishing.com/reuters/CUXAHHXCLRNX7AIU5APRCKWY4A.jpg)
Montenegro's state infrastructure hit by cyber attack -officials

Cybersecurity: Most Online Attacks Rely on Victims Clicking Links

January 2023 Cyber Attacks

The Essential 8 Maturity Model For Cyber Security

Cyber Attack Survival Manual: From Identity Theft to The Digital

5 Ways Big Companies Protect their Data

Is Your Business Attractive to Hackers? Learn the Facts to Protect
Why Protecting Your Customer's Information Is Crucial And How To

An Investigative Update of the Cyberattack - Orange Matter
12 Cybersecurity Best Practices to Prevent Cyber Attacks in 2023

The Cost of a Data Breach for Your Organization
Another Day, Another (Preventable) Data Hack
de
por adulto (o preço varia de acordo com o tamanho do grupo)