XSS by using onclick · Issue #8000 · Dolibarr/dolibarr · GitHub
Por um escritor misterioso
Descrição
Bug The xss filter in "htdocs/main.inc.php" is not enough, we can just use "onclick" and "onscroll" to bypass the filter,eg: <div style="position:absolute;top:0;left:0;width:100%;height:100%" onclick="alert(52)"> , <body onscroll=alert(1
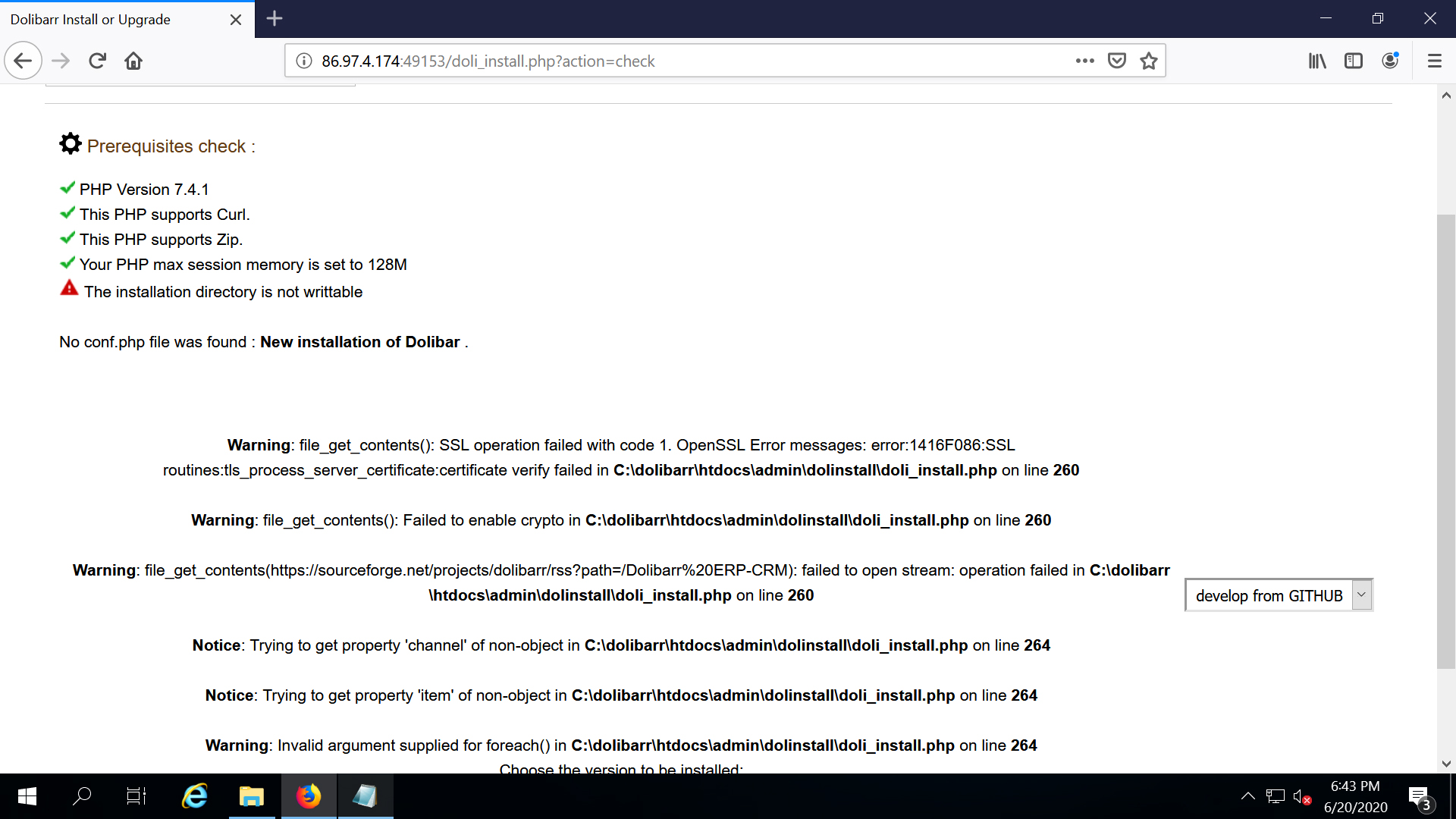
Doli_Install : Dolibarr installation/upgrade script - Installing
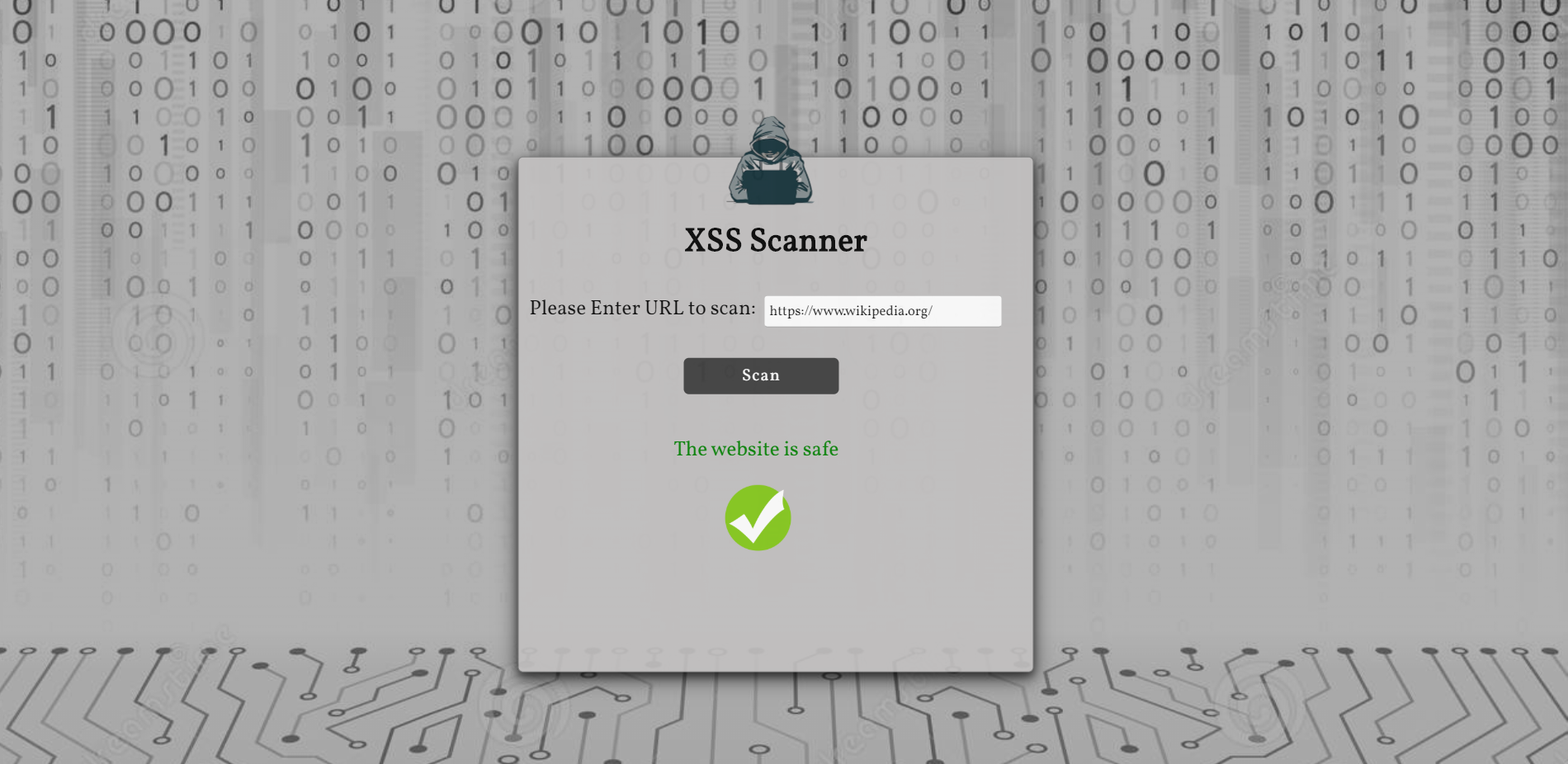
XSS-Scanner - XSS Scanner That Detects Cross-Site Scripting
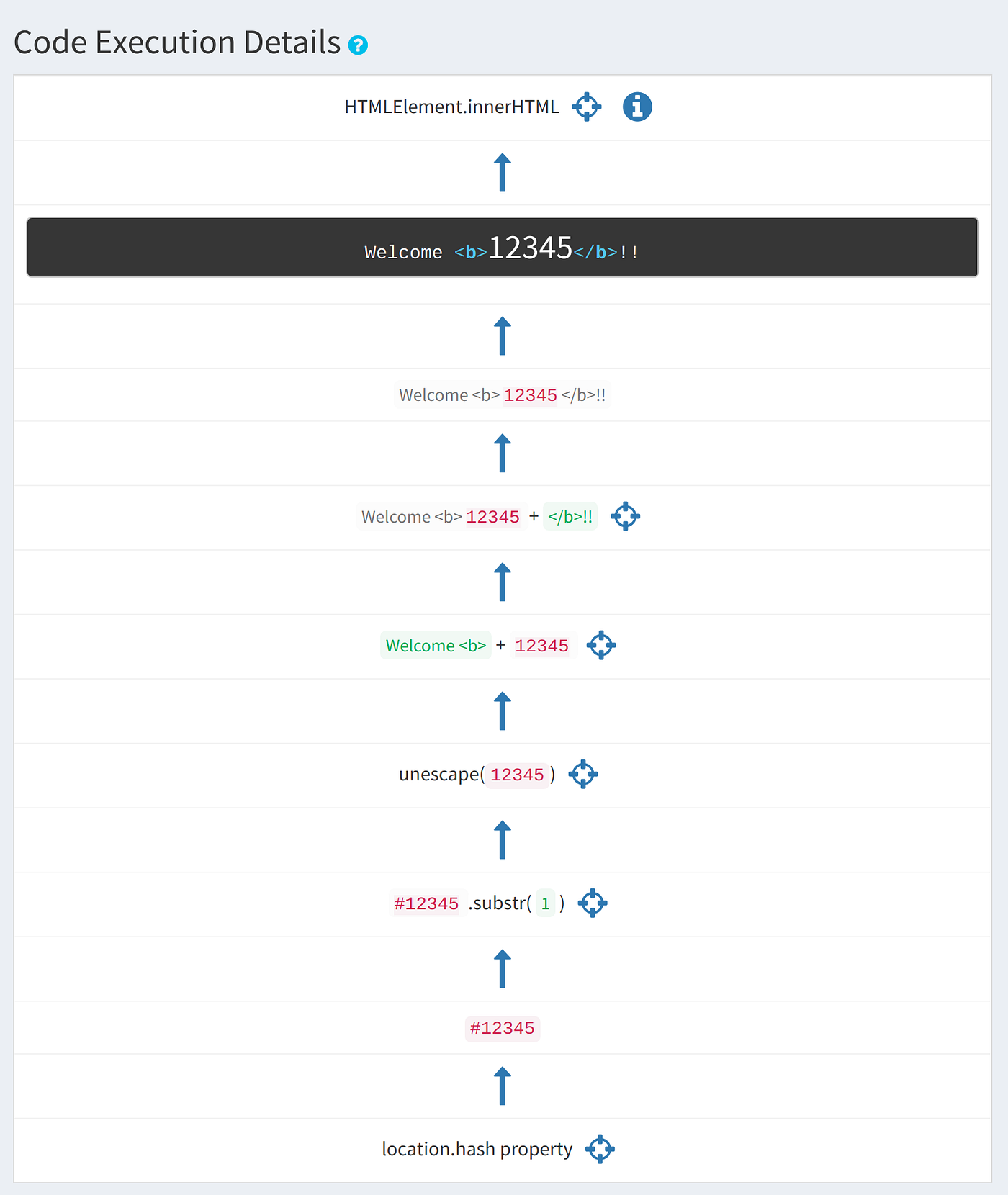
Automating Discovery and Exploiting DOM (Client) XSS
GitHub - s0md3v/AwesomeXSS: Awesome XSS stuff
Update Dolibarr from 3.9.3 to 17 version - Installing my Dolibarr
GitHub - kleiton0x00/XSScope: XSScope is one of the most powerful

XSS-Loader - XSS Scanner and Payload Generator - GeeksforGeeks
GitHub - kleiton0x00/XSScope: XSScope is one of the most powerful
xss · Issue #1 · n00pme/n00pme.github.io · GitHub
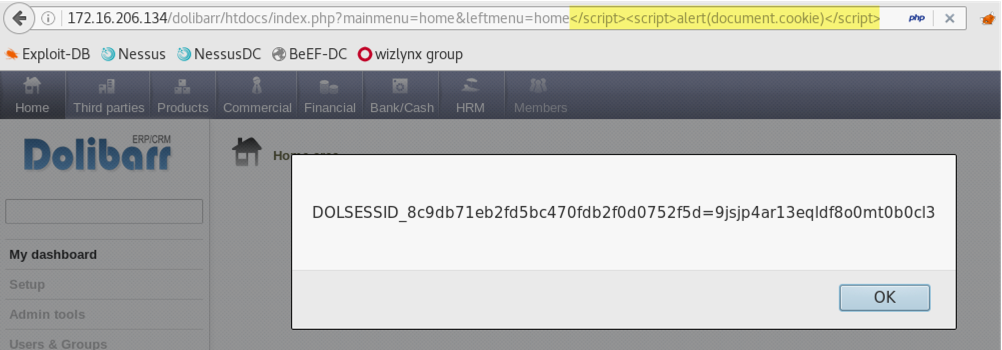
wizlynx group Multiple Reflected & Stored Cross-Site Scripting

Hide 0,00 values in tables (reports) · Issue #21652 · Dolibarr
Issues · Dolibarr/dolibarr · GitHub

GitHub - pratikktiwari/xss: Various scenarios to demonstrate how

Dolibarr on Cloudjiffy - CloudJiffy Blog

xss · Issue #1 · n00pme/n00pme.github.io · GitHub
de
por adulto (o preço varia de acordo com o tamanho do grupo)